
lose 40 lbs by consuming before bed for a week...
February 10, 2025
3:46 am

the fungus will disappear in 1 day! write down an expert's recipe...
February 10, 2025
3:32 am
Toll payment scam: FBI is warning android and iPhone users to delete texts immediately
February 10, 2025
03:51
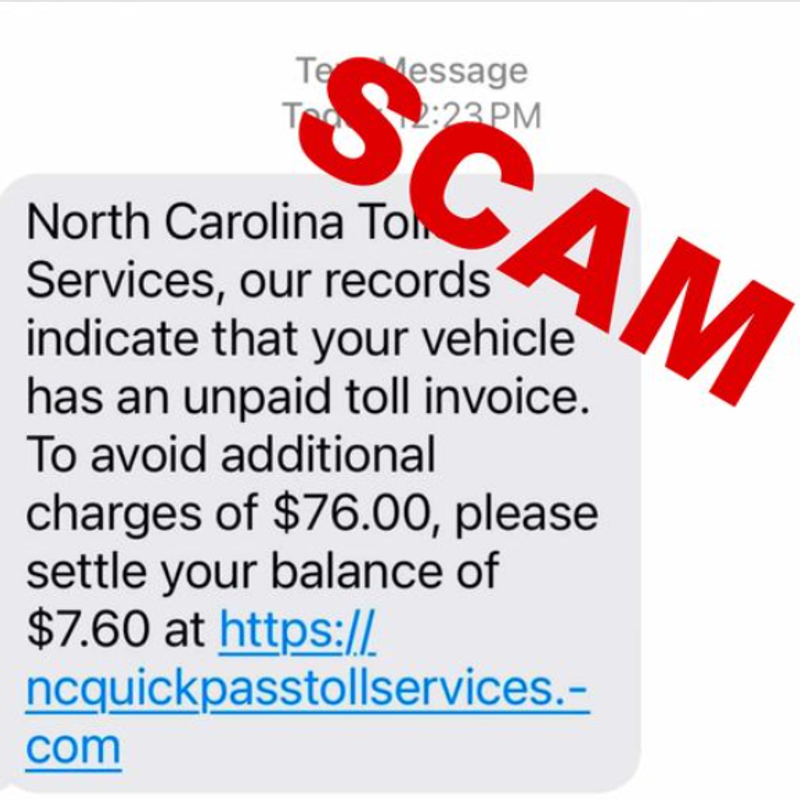
A new nationwide alert from the Federal Bureau of Investigation (FBI) is urging iPhone and Android users across the United States to exercise extreme caution with text messages, particularly those claiming to be from toll authorities. “The scam may be moving from state-to-state,” warns the agency, suggesting that areas currently unaffected could soon become targets.
The sophisticated scheme begins with what appears to be a routine text message from a toll agency, claiming the recipient has outstanding payments that require immediate attention. The scam’s simplicity masks its dangerous nature: victims who click on the provided payment link are directed to a fraudulent page designed to harvest sensitive financial information, including bank account and credit card details.
The Federal Trade Commission (FTC) has joined the FBI in raising awareness about these deceptive messages. “Not only is the scammer trying to steal your money, but if you click the link, they could get your personal info (like your driver’s license number) – and even steal your identity,” the FTC cautions.
Recent Posts

this product is putting plastic surgeons out of work...
February 10, 2025
3:49 am

seer teresa: if you carry them in your pocket, you will have a lot of money...
February 10, 2025
3:49 am

the secret of buddhist monks: how to overcome joint pain....
February 10, 2025
3:29 am

worms come out of you in the morning. try it...
February 10, 2025
3:24 am
The FBI has outlined specific steps for consumers to verify legitimate toll charges:
Intelligence gathered points to Chinese cybercriminal organizations as the primary suspects behind these attacks. These groups have developed sophisticated “commercial phishing kits” that include templates specifically designed to impersonate toll operators across multiple states.
This toll payment scam is part of a larger pattern of cyber threats. The same criminal networks have been observed:
In a notable precedent, December saw the exposure of a Chinese hacking group known as “Salt Typhoon,” which successfully breached major U.S. telecommunications providers, including AT&T, T-Mobile, and Verizon, conducting surveillance operations on their customers.
To combat these evolving threats, FBI officials recommend:
As these scams continue to evolve and spread nationwide, staying informed and maintaining vigilant cybersecurity practices remains crucial for smartphone users.
Recent Posts

In 2023, a strange golden object discovered deep beneath the waters of the Gulf of Alaska captured global attention. Dubbed a “golden egg” because of its smooth, rounded shape and metallic sheen, the object puzzled...
April 23, 2026
12:31 pm

varicose veins and blood clots will disappear very quickly ! at home!...
April 23, 2026
12:13 pm

South Korea’s military is facing renewed scrutiny after an investigation revealed that a 2021 mid-air collision between two fighter jets was caused by pilots taking photos and videos during flight. The Republic of Korea Air...
April 23, 2026
12:19 pm
hair grows 2 cm per day! just do this...
April 23, 2026
12:11 pm
Staying on top of dozens of unread messages can feel like a full-time job. That’s exactly the problem WhatsApp is trying to solve with its upcoming AI-powered chat summaries feature. Currently in development, the tool...
April 23, 2026
12:09 pm

if you find moles or skin tags on your body, read about this remedy...
April 23, 2026
11:51 am
For decades, the United States symbolized opportunity for millions of Indians seeking education, careers, and long-term stability. But that narrative is shifting. A recent survey by the Carnegie Endowment for International Peace, conducted with YouGov,...
April 23, 2026
12:00 pm

i weighed 332 lbs, and now 109! my diet is very simple trick. 1/2 cup of this (before bed)...
April 23, 2026
11:57 am

Iran has reportedly collected its first revenue from tolls imposed on ships passing through the Strait of Hormuz—a move that could reshape not just regional geopolitics, but also the economics of global energy trade. The...
April 23, 2026
11:54 am

doctor: if you have nail fungus, do this immediately...
April 23, 2026
11:34 am

The sudden exit of John Phelan from his post as U.S. Navy secretary has triggered a wave of questions inside Washington and beyond. Officially, the Pentagon described it as a resignation. Unofficially, reports point to...
April 23, 2026
11:47 am

easy ways to get rid of wrinkles at home! (try now)...
April 23, 2026
11:31 am