
people from us those with knee and hip pain should read this!...
April 9, 2026
12:24 pm

stars are now ditching botox thanks to this new product....
April 9, 2026
12:04 pm
One Of China’s Biggest Data Breaches: 10 Petabytes Stolen From Supercomputer
April 9, 2026
12:30
One of the largest alleged cyber intrusions in recent memory is now under scrutiny after claims that a hacker stole more than 10 petabytes of data from a Chinese supercomputing facility. If verified, the China supercomputer data breach would rank among the most consequential digital heists ever, not just for its size but for what may have been exposed.
To grasp the scale, imagine siphoning off the entire storage of over 10,000 high-end laptops. That’s the digital equivalent of draining a lake using a teaspoon, repeatedly, without anyone noticing.
The breach reportedly targeted the National Supercomputing Center in Tianjin, a major state-run hub that supports thousands of research and industrial projects.
Recent Posts

this simple trick removes all parasites from your body!...
April 9, 2026
12:06 pm

i weighed 332 lbs, and now 109! my diet is very simple trick. 1/2 cup of this (before bed)...
April 9, 2026
12:28 pm

if you find moles or skin tags on your body, read about this remedy. genius!...
April 9, 2026
12:29 pm

after reading this, you will be rich in 7 days...
April 9, 2026
12:12 pm
The facility itself is part of a broader national network that underpins China’s ambitions in advanced computing, artificial intelligence, and defense modernization.
Let’s translate the numbers into something tangible.
That means the alleged breach could equal:
Recent Posts

the fungus will disappear in 1 day! write a specialist's prescription...
April 9, 2026
12:06 pm

hair will grow back! no matter how severe the baldness...
April 9, 2026
12:21 pm

varicose veins and blood clots will disappear very quickly ! at home!...
April 9, 2026
12:13 pm

people from america those with knee and hip pain should read this!...
April 9, 2026
12:06 pm
According to cybersecurity researchers who reviewed samples, the dataset spans multiple high-stakes domains.
The data is also said to be linked to major Chinese entities, including:
Some files reportedly carried “secret” classification labels, along with technical schematics and simulation outputs.
Recent Posts

do this twice a day, and everyone will think you have botox!...
April 9, 2026
12:19 pm

worms come out of you in the morning. try it...
April 9, 2026
12:28 pm
a spoon on an empty stomach burns 26 lbs in a week...
April 9, 2026
12:18 pm

read this immediately if you have moles or skin tags, it's genius...
April 9, 2026
12:29 pm
Ironically, the attack may not have relied on cutting-edge hacking techniques.
This slow-drip strategy is key.
Instead of triggering alarms with large transfers, the attacker reportedly:
Recent Posts

seer teresa: if you carry them in your pocket, you will have a lot of money...
April 9, 2026
12:14 pm

doctor: Іf you have nail fungus, do this immediately...
April 9, 2026
12:21 pm

this method will instantly start hair growth...
April 9, 2026
12:17 pm

varicose veins and blood clots will disappear very quickly ! at home!...
April 9, 2026
12:18 pm
It’s less like a smash-and-grab robbery and more like quietly emptying a vault, one envelope at a time.
Large systems like supercomputing centers are designed for heavy data movement. That creates a paradox.
As noted by cybersecurity experts, small, consistent data transfers can easily blend into normal operations.
Recent Posts

i did this and my knees and joints haven’t hurt for 10 years now....
April 9, 2026
12:03 pm

always look young. this product removes wrinkles instantly!...
April 9, 2026
12:20 pm

worms come out of you in the morning. try it...
April 9, 2026
12:09 pm
i weighed 332 lbs, and now 109! my diet is very simple trick. 1/2 cup of this (before bed)...
April 9, 2026
12:00 pm
Not fully.
This uncertainty is typical in large-scale cyber incidents, where verification lags behind claims.
If even a fraction of the claims are accurate, the consequences could be significant.
Recent Posts
if you find moles or skin tags on your body, read about this remedy. genius!...
April 9, 2026
12:26 pm

seer teresa: if you carry them in your pocket, you will have a lot of money...
April 9, 2026
12:04 pm

the fungus will disappear in 1 day! write down an expert's recipe...
April 9, 2026
12:03 pm
hair grows 2 cm per day! just do this...
April 9, 2026
12:06 pm
In particular, access to simulation data and TTP-like methodologies could offer insights into how systems are designed, tested, and deployed.
The incident highlights a recurring theme in major breaches: complexity creates opportunity.
Rather than a failure of advanced defenses, this appears to be a failure of fundamentals.
Recent Posts

varicose veins and blood clots will disappear very quickly ! at home!...
April 9, 2026
12:29 pm
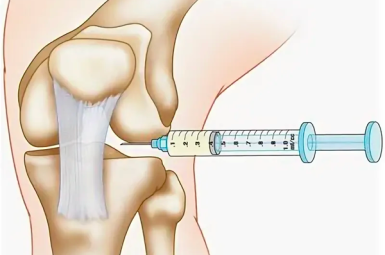
people from us those with knee and hip pain should read this!...
April 9, 2026
12:26 pm

a young face overnight. you have to try this!...
April 9, 2026
12:04 pm

this simple trick removes all parasites from your body!...
April 9, 2026
12:11 pm
While comparisons are still emerging, this breach stands out for scale.
It shifts the narrative from cybercrime to cyber-espionage.
Several developments will determine the true impact of the China supercomputer data breach.
Governments and organizations worldwide will likely treat this as a case study in what not to overlook.
Recent Posts

Apple is preparing to kick off its annual Worldwide Developers Conference (WWDC) on June 8, with the five-day event expected to showcase the company’s biggest software and AI upgrades yet. Held at Apple Park in...
June 4, 2026
11:54 am

lose 40 lbs by consuming before bed for a week...
June 4, 2026
11:27 am

Wildlife officials across parts of the southern United States are asking residents to report — and in some cases kill — a fast-growing invasive species that experts say poses a serious threat to local ecosystems....
June 4, 2026
11:47 am

if you find moles or skin tags on your body, read about this remedy. genius!...
June 4, 2026
11:34 am

Chinese hardware start-up Monako is betting that the next big computing platform won’t sit on your desk or in your pocket. It will sit on your face. The company recently unveiled Monako Glass, a lightweight...
June 4, 2026
11:40 am

this is a sign! money is in sight! read this and get rich....
June 4, 2026
11:15 am

Peter Phillips is preparing to marry Harriet Sperling in what sources describe as an intimate private ceremony set for June 2026. But one notable royal name is expected to be missing from the guest list:...
June 4, 2026
11:32 am

doctor: Іf you have nail fungus, do this immediately...
June 4, 2026
11:27 am

Taiwan is rapidly expanding one of the most important pillars of its defense strategy: anti-ship missiles. Taiwan is building a new strategy to counter China, calling it the “kill zone” strategy. According to a Reuters...
June 4, 2026
11:19 am

this method will instantly start hair growth...
June 4, 2026
10:52 am

As Brazil’s national team departed for the 2026 FIFA World Cup, an unusual sight unfolded on the runway at Rio de Janeiro’s Galeão International Airport. Moments before takeoff, the aircraft carrying Brazil’s squad, including superstar...
June 4, 2026
11:17 am

varicose veins will disappear in the morning! read!...
June 4, 2026
11:00 am